Welcome to the third tutorial in this series about installing WordPress and a performant server stack on an Alibaba ECS Cloud Instance.
In the previous two tutorials, we provisioned and secured our Ubuntu 16.04 server installation, then completed the LEMP stack with NGINX, MariaDB and PHP7. Today we are going to configure a Domain to work with our server, and secure everthing with an SSL certificate so our final WordPress site can only be accessed via HTTPS. In the next tutorial we will complete the series by installing WordPress, and configuring transactional emails.
As with all of these tutorials, the instructions should generally stand for any of the main cloud providers. This tutorial has some steps specific to Alibaba Cloud, mainly regarding configuring the security group for inbound access to port 443, but they are minor and can be skipped over for other providers.
A few words about Domain Registration
Many people will register a domain through their hosting company, I recommend against that. I much prefer to keep my domain registration and hosting separate, this provides a more robust framework in case of unseen problems with your hosting providers infrastructure. That is to say, if your hosting goes down but your domain is registered elswhere, then it is very easy to just change your nameservers and get your site back online quickly.
I recommend Namecheap or iwantmyname for domain registry, they are primarily domain registrars and resolve DNS and Nameserver changes quickly.
It goes without saying that you’ll need to have a registered domain to use for this tutorial, in my case I have a domain registered with Namecheap specifically for testing purposes and tutorials, the aptly chosen an-example-domain.com
Part One – Configuring your Domain
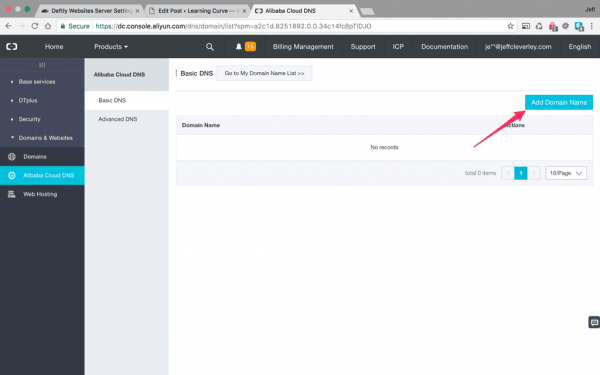
Step 1. Add a Domain to Alibaba Cloud DNS
Visit your Alibaba ECS console and make your way to the Alibaba Cloud DNS section. Then click the blue button in the top left to add a Domain Name:
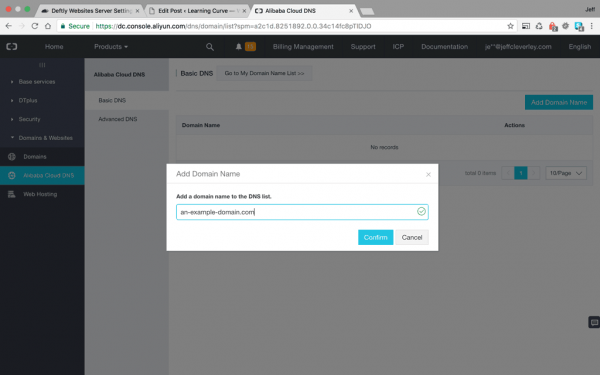
A pop up box will appear with a text entry field, enter your domain name here and confirm:
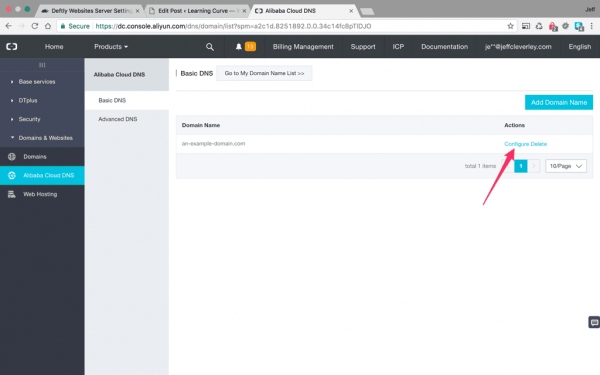
Your domain will now appear in the list of Domain Names in the Alibaba Cloud DNS settings page.
Now we need to configure some DNS records to get everything working properly. Click the configure link that is highlighted in the screenshot below:
The link will take you to a configurations page where you can add your DNS records:
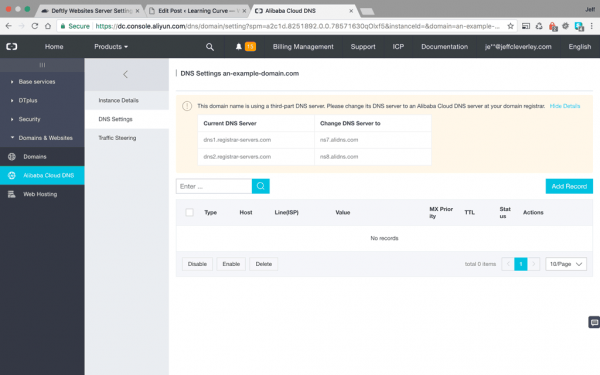
In my case, as mentioned earlier, my domain is registered with a third party domain registrar, that means my domain is using my registrar’s domain name server. As you can see in the screenshot above, Alibaba cloud DNS immediately checks the records and throws a warning telling me that I need to change my domain’s nameservers.
Step 2. Change Nameservers at your domain registrar
To do that, go to your domain registrar and locate the setting for DNS. Somewhere in the settings there will be a button for ‘Change Nameservers’ or ‘Use Custom Nameservers’, or something similar. With my domain at Namecheap it’s found in a dropdown called ‘Custom DNS’ under the ‘Nameservers’ setting, illustrated below:
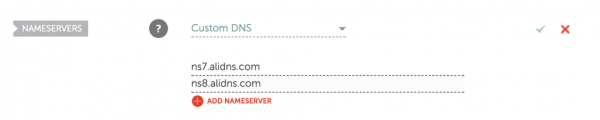
Enter the nameservers provided by Alibaba and click save.
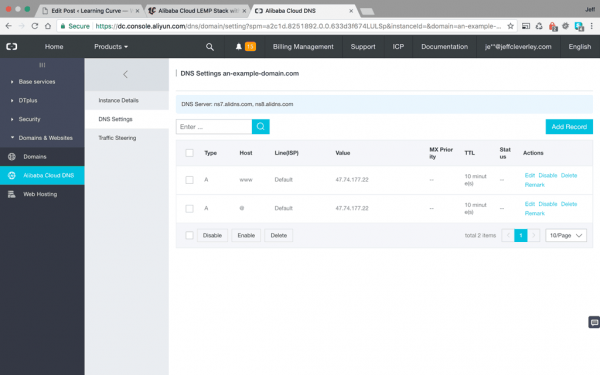
Step 3. Enter DNS records
Now return to the Alibaba Cloud DNS settings page, and add DNS records for your domain. For this tutorial we are only adding two A records. A records are for your server’s ipv4 address, if this were a production site you would also need to add matching AAAA records for ipv6 address, and several other records, such as an MX record for your email server etc.
Add one type A record for the Host @, and another for the Host www. The shortest TTL (Time Till Live) setting allowed by Alibaba’s DNS system is 10 minutes, which means that these changes will take at least that long to take effect on their end, although for changes to propagate across the internet can take up to 24 hours or more.
Your settings should look something like this:
Did I mention that I find that changes in DNS settings made with dedicated domain registrars tend to propagate faster than with hosting providers? I did, my apologies for belaboring a point.
In any case, you can check to see if your DNS changes have propagated with a service like whatsmydns.com or by using the Domain Information Groper dig terminal command.
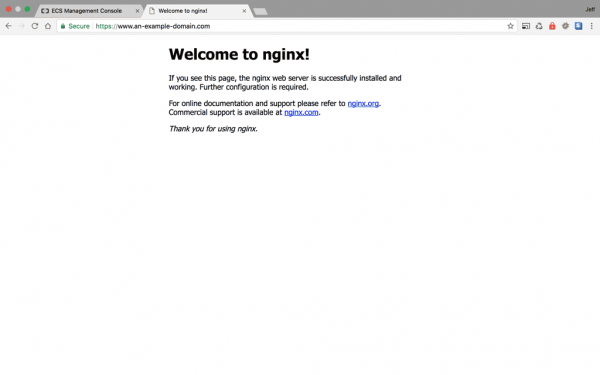
Step 4. Test your domain
Once these changes have propagated you should be able to visit your site by using the domain, with or without the www subdomain:
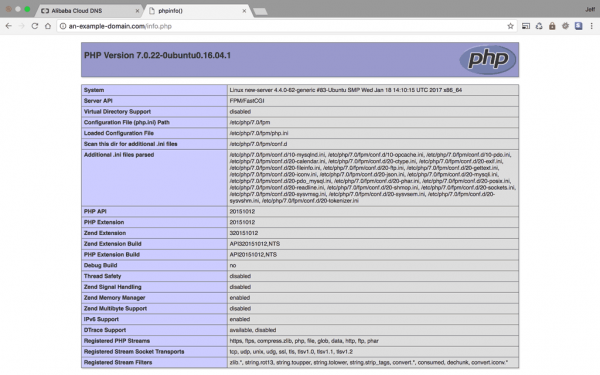
Now we have our domains configured properly so we can visit our server with a url, we can begin to install our SSL certificates.
Part Two – Securing NGINX with Let’s Encrypt SSL certificates
The web is moving towards a more secure future. SSL certificates protect visitors of your site by enabling HTTPS encryption on web servers. In the past SSL certificates were a moderately expensive addition to your hosting deemed only necessary for eCommerce sites or other sites that transmitted sensitive information.
Things have changed since those days, now it is considered best practice in web development to secure all sites with an SSL certificate. This has additional benefits to just increasing security, the latest generation of the HTTP protocol, HTTP/2, requires an SSL certificate to be installed before it can be used. HTTP/2 can dramatically increase the speed of a well configured site due to a range of improvements such as Single Connection Loads, Multiplexing, Header Compression, and more. You can find out more about HTTP/2 here.
There is also the not inconsequential matter that sites without SSL certificates are now being penalised by Google, with Chrome even throwing warnings for unsecured sites.
Let’s Encrypt is a free, automated, and open certificate authority (CA) provided by the Internet Security Research Group, they have almost single-handedly accelerated the widespread adoption of SSL certificates in recent years, we should all be very grateful.
We will be using the Let’s Encrypt Certbot to obtain a free SSL certificate, Certbot is an awesome package that will automatically make most of the necessary NGINX configuration changes.
Step 5. Configuring Ubuntu to enable access to external repositories
We will be installing the certbot software from Let’s Encrypt’s separate external repository. That means we will need to add a new repository to our apt package manager.
Unfortunately our Instance’s Ubuntu installation doesn’t have the required package installed to allow us to add external repositories.
Not to worry, that’s a quick fix, just enter the following command to install said package:
$ sudo apt-get install -y software-properties-common
Step 6. Installing Certbot
With that additional package we can now install certbot with the following commands.
To add the repository:
$ sudo add-apt-repository ppa:certbot/certbot
Then update the package list to pick up the new repository’s package information:
$ sudo apt-get update
And finally, install certbot with apt-get:
$ sudo apt-get install python-certbot-nginx
Now Certbot is ready to use, but before we can use it, we need to configure NGINX some more.
Step 7. Setting up NGINX to serve domains
Yes I know, I did say Certbot can automatically configure the SSL for NGINX and add the necessary settings in the NGINX configuration file server block. But before it can do that NGINX needs to be configured for your domain name, at present it is only configured for an IP address.
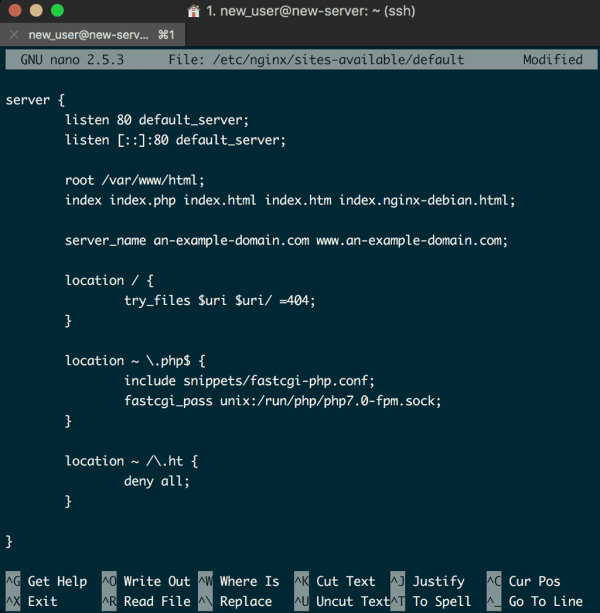
Let’s update the config file:
$ sudo nano /etc/nginx/sites-available/default
Now replace the servers ipv4 address on the server_name line with your domain name, remember to add both the domain with and without www :
server_name an-example-domain.com www.an-example-domain.com;
Your NGINX default config file server block should look something like the following:
Since the NGINX config file has been changed, it should be checked for syntax errors again:
$ sudo nginx -t
All being well, reload it to load in the new configuration:
$ sudo systemctl reload nginx
With these changes made, Certbot will now be able to locate the correct server block and update it automatically.
Next we’ll update the UFW firewall to allow HTTPS traffic.
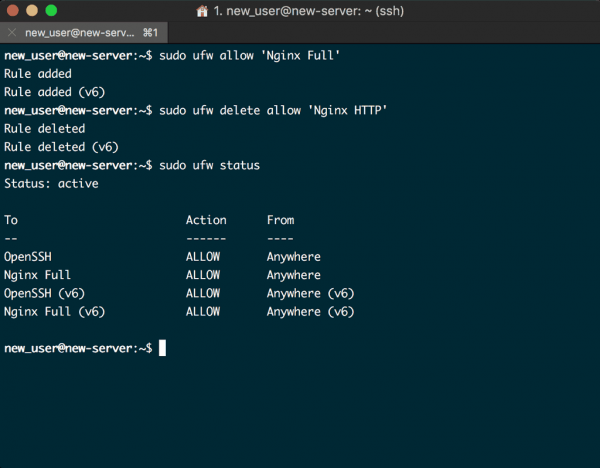
Step 8. Updating the UFW Firewall
The UFW firewall we configured previously in the series has only been configured for HTTP connections, this now needs adjusting to allow HTTPS traffic.
To do this we will allow ‘Nginx Full’ first:
$ sudo ufw allow 'Nginx Full'
And then delete the redundant ‘Nginx HTTP’ profile that we previously allowed:
$ sudo ufw delete allow 'Nginx HTTP'
Finally, check the firewall status with:
$ sudo ufw status
Your terminal should output the following:
With our firewall configured properly, we would normally be ready to obtain our SSL certificate, but Alibaba Cloud Hosting is a little bit different however.
Step 9. Configure Alibaba Cloud Security Group for HTTPS connections
Remember all that time ago, when we first provisioned the ECS instance, we added it to a Security Group? That is Alibaba Cloud nonmenclature for their firewall, so that’s where we need to go now.
In the Alibaba Cloud Security Groups, you will see the default security group you attached, click the link to configure it’s rules:
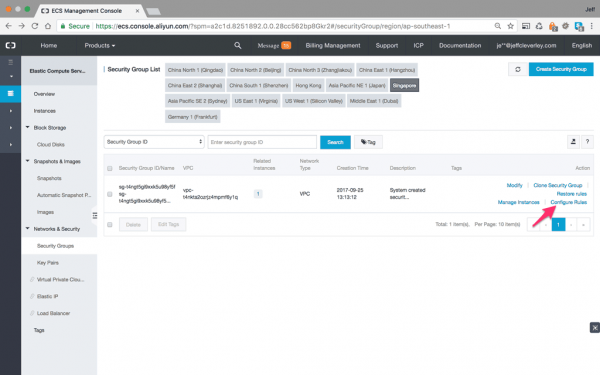
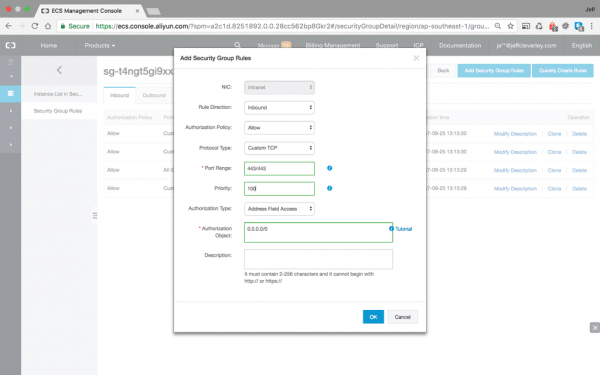
For HTTPS connections with an SSL, we need our server to be listening on Port 443. Currently the security group has no rule configured to allow inbound connections to the server on this port.
Add a rule for Port 443 as follows:
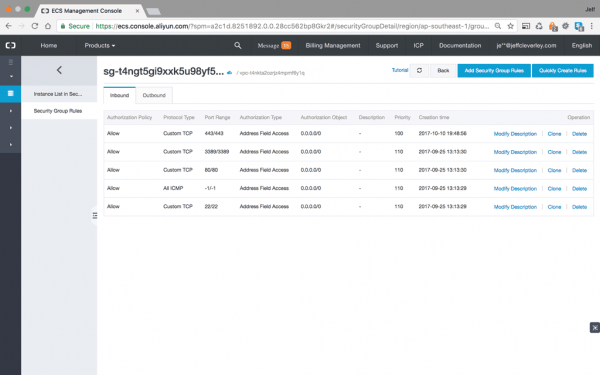
Now we’re ready to run Certbot to obtain and configure our SSL certificates, and configure server settings.
Step 10. Obtaining a Let’s Encrypt SSL Certificate
We will use Certbot’s NGINX plugin to obtain an SSL certificate for our domain, it will automagically take care of configuring NGINX and reloading the config when necessary. Enter the following command, using your own domain name:
$ sudo certbot --nginx -d domain.com -d www.domain.com
This command runs certbot with the aforementioned –nginx plugin, and uses -d to specify the domain names for which the certificate will be valid.
If everything was succesful certbot will check to verify you control your domain, and upon verification will issue your certificate and ask you how you would like to configure your HTTPS settings:
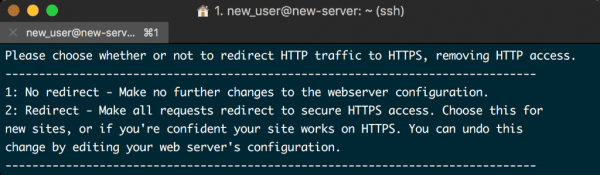
I recommend to configure the redirects so that all traffic is served via HTTPS.
At this point you will be able to access your site using https://, and you will get the reassuring green lock and security indicator.
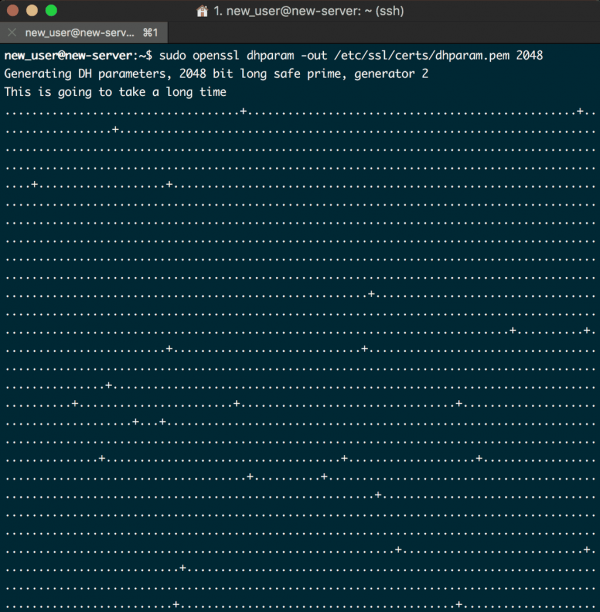
Step. 11 Increase SSL security – Update Diffie-Hellman Parameters
Even though your site is secured with an SSL, it is using weak Diffie-Hellman parameters which means that the initial key exchange is still more vulnerable than we may wish.
To fix this create a new dhparam.pem file and add it to the server block.
Create the file using openssl:
$ sudo openssl dhparam -out /etc/ssl/certs/dhparam.pem 2048
This may take some time, and will look like this:
When this process is complete, open up the default sites NGINX config file again:
$ sudo nano /etc/nginx/sites-available/default
And paste in the following code, this can be anywhere inside the server block:
ssl_dhparam /etc/ssl/certs/dhparam.pem;
The entire server block should look like the following, notice the SSL configuration settings that have also been added by certbot:
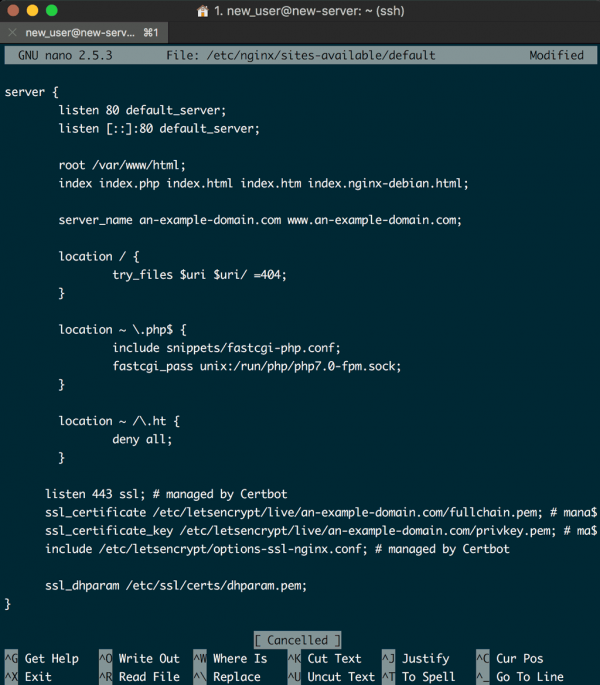
Save the file and close the editor. And since we have altered the NGINX configuration again, we will need to check the syntax again:
$ sudo nginx -t
If there are no errors, reload NGINX:
$ sudo systemctl reload nginx
The site is now a lot more secure. You can test it using the SSL Labs Server Test, and it should get an A rating.
Step 12. Setting up Certificate Auot Renewal with a Cron job
Let’s encrypt certificates are currently only valid for 90 days to encourage users to automate their certificate renewal process, which is exactly what we are going to do.
To do this we will use a cron job. This is the system Linux uses for running periodic system jobs. To add a cron job we must edit a file called a crontab:
$ sudo crontab -e
The text editor will open the default crontab, paste the following code at the end of the file, then save it and close it:
0 0 * * * /usr/bin/certbot renew --quiet
This means run this /usr/bin/certbot renew –quiet command at this 0 0 * * * time.
0 0 * * * translates to every day at midnight. To find out more about cron timings you can visit CronTab.Guru.
The renew command for Certbot will check all certificates installed on the system and update any that are set to expire in less than thirty days.
The –quiet command tells Certbot not to wait for user input, or output any information.
Your SSL certificate is now installed, has an A rating, and is configured to renew automatically. Time to test things out.
Step 13. Test your server for HTTPS connection
You should now be able to visit your website by visiting your domain using https:
https://an-example-domain.com
or
https://www.an-example-domain.com
And we’re done.
Your ECS instance should now have a fully installed LEMP stack, with a domain configured, and a secure SSL certificate installed.
Next up… The final tutorial in this series, let’s get us some WordPress going on.
See you then
Jeff
Leave a Reply